You are trying to perform a network analysis and filter out the traffic from a specific source and a specific applications, but Wireshark isn’t helping. Then you try Microsoft Message Analyzer which has many filters and modules to be specific on your research.
Here’s a simple way to filter the source IP address and the name of the application process. Download Microsoft Message Analyzer and run is as an Administrator. For this example I am using “192.168.1.7” as my source IP and “vivaldi.exe” as application process name. So you will have to change it accordingly.
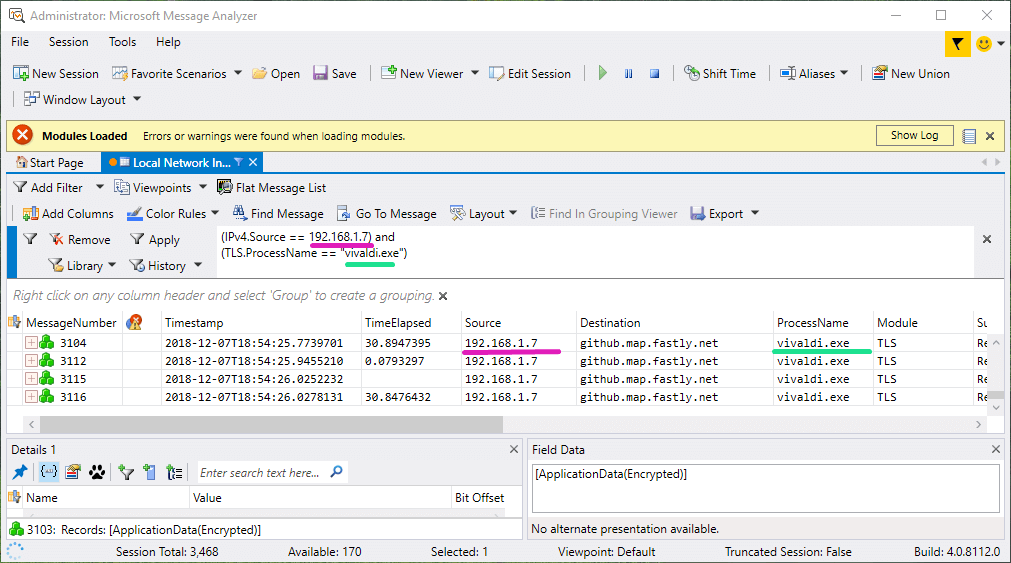
The “IPv4.Source” refers to the source of the request. and “TLS.ProcessName” refers to the name of the process.
Here’s how to do step-by-step:
- Start a Local Trace
- Once the application begins to display network analysis
- Add this filter in the filter box
(TLS.ProcessName == "vivaldi.exe") - Apply the filter and now you’ll see the filtered network traffic
Additionally use the “(IPv4.Source == 192.168.1.7)” filter to filter your own IP. This is helpful when you are trying to analyze an application for malicious traffic or just to check where the application is sending and receiving data from.